Warning: this is part five of what is intended to be a nine-part blog looking and expanding on what identity is!
If you have arrived here directly, then please go back and start at part 1 - after all, in the Identity world context is everything! [sorry for the identity in-joke].
https://www.globalidentity.blog/2022/11/mistaken-identity-part1.html
Part Five - Why privacy and anonymity must be at the heart of your digital identity ecosystem
There are two famous (prophetic, as they are now over twenty years old,) quotes about tech and privacy:
“The privacy you’re concerned about is largely an illusion. All you have to give up is your illusions, not any of your privacy.” Oracle CEO Larry Ellison in 2001
“You have zero privacy anyway. Get over it.” SUN Microsystems CEO Scott McNealy in 1999.
If you do not already subscribe, then Have I Been Pwned? allows you to search across multiple data breaches to see if your email address or phone number has been compromised. At the last count my personal data has been exposed in seventeen major breaches; everything from date-of-birth, to home address and phone numbers.
And that’s before you perform a dark-web trawl on your name / job / company, and that’s even more scary.
Which leads us to the first (linked) conclusions:
If all your attributes are known, then what you should actually care about is: someone else being able to assert them as “proof” they are you.
When someone/something asserts that they are a particular entity (“hello I’m from your bank”) how can you verify the veracity of said assertion?
However, there are areas of your life where a failure of privacy is hazardous to your life: for example one of our collaborators is an Iraqi Kurd who lived in Iraq during the reign of Saddam Hussain; or that you have a subscription to “Gay Times” if you are living/working in Afghanistan; both attributes (or whole persona) that containing SPI (Sensitive Personal Information).
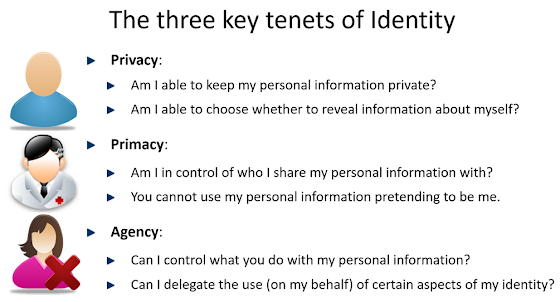
Which leads us to the first three tenets for privacy;
However, to ensure an ecosystem with privacy at its core; then THE fundamental design principle is the need for 100% anonymity at the root of any identity.
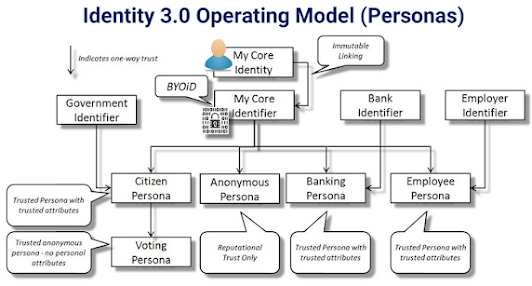
Though counter-intuitive to most identity and security professionals, it’s actually fairly obvious; that if you want to be able to issue linked assertions from disparate personas (see part four), then:
There must be a common root; AND
Only said entity must be in sole control of it; AND THEREFORE
It must be known and accessible only to that entity.
In addition, using this root of trust to make linked assertions, then the relying party (the entity receiving and needing to verify the linked assertion) must also understand the method by which the issuing entity is linked (the level of immutable linkage) to the root of trust; thus, they are able to factor this into their risk-equation for the transaction.
In real-life, you are your own Core Identity, and the immutable linkage between you and the assertion(s) is generally an approved photo ID (Entity:person → photo → name → matched attribute assertions).
Implementing this in the digital realm, there needs to be a known linkage between the entity:person with their “Core Identity” and their “Core Identifier” (their 100% anonymous “cryptographic root of trust”).
In part six, I will look at why understanding the “locus-of-control” problem is fundamental to proposing any solution in the identity ecosystem space.
https://www.globalidentity.blog/2023/02/mistaken-identity-part6.html
References:
https://www.globalidentityfoundation.org/downloads/Identity_30_Definitions.pdf
https://www.globalidentityfoundation.org/downloads/Identity_30_Principles.pdf
https://collaboration.opengroup.org/jericho/Jericho%20Forum%20Identity%20Commandments%20v1.0.pdf
https://www.globalidentityfoundation.org/downloads/Primer_-_Anonymity_at_root_of_an_Identity.pdf

No comments:
Post a Comment